Related search
Televisions
Chargers
Beanies
Manufacturing Machine
Get more Insight with Accio
Android Security Bulletin Crisis: 129 Vulnerabilities Rock Retail
Android Security Bulletin Crisis: 129 Vulnerabilities Rock Retail
8min read·James·Mar 9, 2026
The March 2026 Android Security Bulletin delivered a sobering wake-up call to electronics retailers worldwide with its record-breaking 129 vulnerabilities, including the actively exploited CVE-2026-21385 zero-day flaw. This high-severity vulnerability impacts 235 different Qualcomm chipsets across smartphones, tablets, and foldables from major manufacturers including Samsung, Xiaomi, OnePlus, Motorola, and Nokia. The integer overflow flaw allows local attackers to trigger memory corruption and potentially gain elevated system privileges, creating immediate security concerns for millions of Android devices currently sitting in retail inventory.
Table of Content
- Mobile Security Crisis: The Zero-Day Dilemma for Retailers
- The Mobile Device Supply Chain Under Threat
- Practical Approaches for Electronics Wholesalers
- Transforming Security Challenges into Sales Opportunities
Want to explore more about Android Security Bulletin Crisis: 129 Vulnerabilities Rock Retail? Try the ask below
Android Security Bulletin Crisis: 129 Vulnerabilities Rock Retail
Mobile Security Crisis: The Zero-Day Dilemma for Retailers

Electronics sellers now face unprecedented inventory management challenges as they navigate customer concerns about device security while maintaining profitable operations. The vulnerability’s widespread impact across multiple hardware configurations means that retailers must quickly assess which devices in their current stock require immediate security updates versus those that can be safely sold with existing firmware. Google’s Threat Analysis Group confirmed “limited, targeted exploitation” of CVE-2026-21385, transforming what might have been a routine security update into an active business crisis requiring immediate strategic response from electronics retailers and wholesalers.
Android March 2026 Security Bulletin: Critical Vulnerabilities
| CVE ID | Component | Severity & Type | Affected Versions/Details |
|---|---|---|---|
| CVE-2026-21385 | Qualcomm Display | High (Active Exploitation) | Limited, targeted exploitation in the wild; time-sensitive patching advised. |
| CVE-2026-0006 | Media Codecs Mainline | Critical (Remote Code Execution) | Android 16; allows RCE without privileges or user interaction. Patchable via Google Play. |
| CVE-2025-48631 | System | Critical (Denial-of-Service) | Android 14, Android 15, Android 16, and Android 16-QPR2. |
| CVE-2026-0047 | Framework | Critical (Privilege Escalation) | Specifically affects Android 16-QPR2. |
| CVE-2026-0037, CVE-2026-0027, CVE-2026-0028, CVE-2026-0030, CVE-2026-0031 | Protected Kernel-Based Virtual Machine (pKVM) | Critical (Elevation of Privilege) | Multiple flaws impacting the pKVM subsystem. |
| CVE-2024-43859 | Flash-Friendly File System (F2FS) | Critical | Kernel-level vulnerability addressed by 2026-03-05 patch. |
| CVE-2026-0038 | Hypervisor | Critical | Kernel-level vulnerability addressed by 2026-03-05 patch. |
| CVE-2026-0114, CVE-2026-0120, CVE-2026-0122 | Modem / Baseband | Critical (Remote Code Execution) | Pixel-only vulnerabilities fixed in the March 2026 update. |
| CVE-2024-56184 | Bootloader | Critical (Elevation of Privilege) | Pixel-specific issue affecting device boot process. |
The Mobile Device Supply Chain Under Threat
The March 2026 security crisis exposed critical vulnerabilities in mobile device supply chain management, with 10 critical severity flaws requiring no user interaction to execute remote code execution or privilege escalation attacks. These vulnerabilities, ranging from CVE-2026-0006 in System components to CVE-2025-48631 causing denial-of-service conditions, demonstrate how quickly security threats can cascade through global electronics inventory systems. The bulletin’s dual security patch levels of 2026-03-01 and 2026-03-05 created additional complexity for retailers managing Android Open Source Project versions 14, 15, 16, and 16-qpr2 across different device categories.
Device management professionals now must navigate a 78-day window from Google’s initial December 18, 2025 alert to Qualcomm through the March 3, 2026 public patch release, highlighting the extended vulnerability exposure period that affects inventory turnover strategies. The inclusion of fixes for components from MediaTek, Arm, Unisoc, and Imagination Technologies means that retailers must evaluate security patch availability across multiple hardware ecosystems simultaneously. This multi-vendor complexity requires sophisticated inventory tracking systems to identify which devices receive immediate security updates versus those requiring extended manufacturer testing periods.
Identifying Affected Inventory: A 129-Vulnerability Challenge
Retailers must immediately audit inventory containing the 235 affected Qualcomm chipsets, as CVE-2026-21385 represents just one critical flaw among 129 total vulnerabilities requiring urgent patches. The seven critical escalation of privilege flaws within Kernel components, combined with CVE-2026-0047 in Framework components, create multiple attack vectors that sophisticated threat actors can exploit across different device configurations. Electronics buyers need comprehensive vulnerability assessment tools to identify which smartphones, tablets, and foldable devices in their current stock face the highest security risks from these newly disclosed flaws.
The 78-day timeline from Google’s Threat Analysis Group discovery on December 18, 2025, to the March 3, 2026 bulletin release created an extended period where affected devices remained vulnerable in retail channels. Qualcomm’s February 2, 2026 customer notification provided manufacturers with only 29 days to develop, test, and distribute security patches before public disclosure. This compressed timeline means that retailers selling devices from Samsung, Xiaomi, OnePlus, Motorola, and Nokia must implement rapid inventory assessment protocols to distinguish between patched and unpatched device stock in their warehouses and retail locations.
Managing Customer Security Expectations
Google Pixel devices receive immediate security updates directly from Google, while other Android manufacturers require additional testing time to adapt patches for specific hardware configurations before distribution to end users. This patch availability gap creates a two-tiered security environment where Pixel device buyers gain immediate protection while customers purchasing Samsung, Xiaomi, or OnePlus devices may wait weeks or months for equivalent security coverage. Retailers must develop clear communication strategies that explain these manufacturer-specific patch deployment timelines without undermining customer confidence in non-Pixel Android devices.
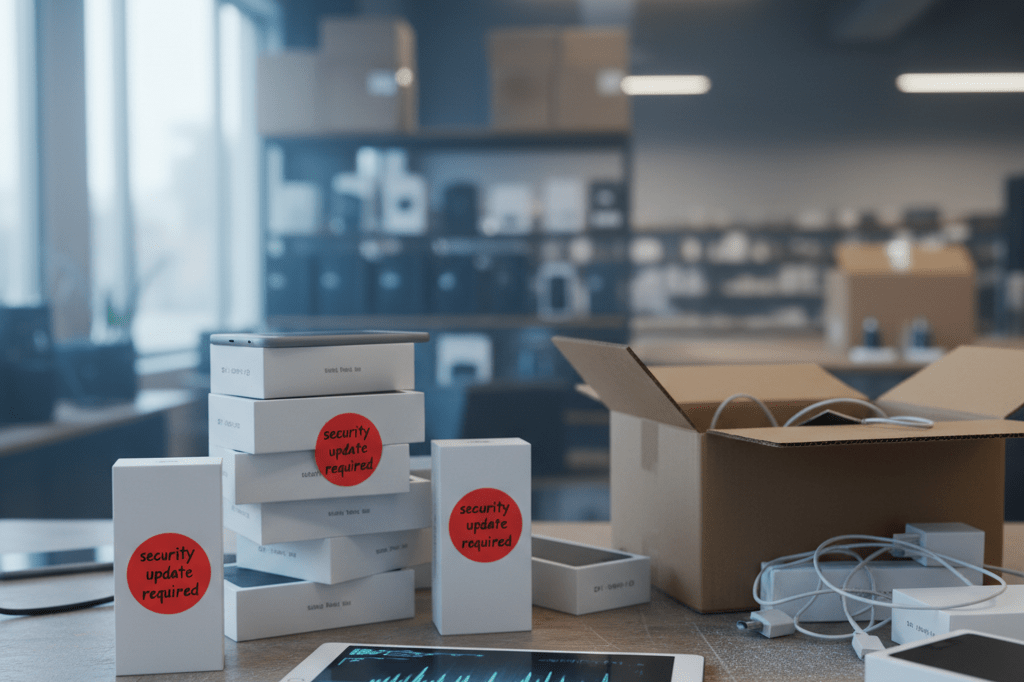
The “limited, targeted exploitation” status of CVE-2026-21385 requires retailers to balance honest security disclosure with maintaining customer trust in Android device reliability and manufacturer responsiveness. Electronics sellers should implement transparent inventory labeling systems that identify devices with current security patches versus those awaiting manufacturer updates, allowing customers to make informed purchasing decisions. Since previous zero-day vulnerabilities CVE-2025-48633 and CVE-2025-48572 were patched in December 2025, retailers can reference this successful remediation history to demonstrate the Android ecosystem’s capacity for rapid security response while acknowledging current patch deployment challenges across different hardware vendors.
Practical Approaches for Electronics Wholesalers

The March 2026 Android security crisis created an immediate need for electronics wholesalers to develop comprehensive response strategies that address both inventory management and customer relationship challenges. Wholesalers managing devices affected by CVE-2026-21385 and the additional 128 vulnerabilities must implement systematic approaches that distinguish between the 2026-03-01 and 2026-03-05 patch levels while maintaining profitable operations. These practical strategies enable wholesale electronics distributors to transform security vulnerabilities from operational headaches into competitive advantages through transparent communication and value-added services.
Forward-thinking wholesale operations are leveraging the 235 affected Qualcomm chipsets as an opportunity to demonstrate superior inventory management capabilities and security expertise to their retail partners. The complexity of managing Android Open Source Project versions 14, 15, 16, and 16-qpr2 across multiple manufacturer ecosystems requires wholesalers to develop sophisticated tracking systems that can identify patch status in real-time. Successful implementation of these strategies allows wholesalers to maintain customer confidence while navigating the extended vulnerability windows that affect devices from Samsung, Xiaomi, OnePlus, Motorola, and Nokia manufacturers.
Strategy 1: Implement Systematic Security Update Verification
Electronics wholesalers must establish comprehensive mobile device security verification systems that can rapidly distinguish between devices carrying the 2026-03-01 versus 2026-03-05 patch levels across their inventory streams. The dual patch release structure means that devices receiving only the initial 2026-03-01 update lack critical fixes for closed-source third-party and kernel subcomponents that were included in the more comprehensive 2026-03-05 release. Wholesalers should implement barcode scanning systems integrated with manufacturer patch databases to automatically flag devices requiring security updates, ensuring that the 10 critical severity vulnerabilities and 7 kernel privilege escalation flaws are properly addressed before distribution to retail partners.
Third-party security certification programs provide additional verification layers for patched inventory management, particularly when dealing with the complex hardware configurations from MediaTek, Arm, Unisoc, and Imagination Technologies components. Documentation processes must track patch deployment timelines across the 78-day window from Google’s December 18, 2025 discovery through the March 3, 2026 public release, enabling wholesalers to provide detailed security status reports to their retail customers. Advanced wholesalers are partnering with cybersecurity firms to offer device security verification certificates that demonstrate compliance with the latest Android security patches, creating additional value for retailers concerned about inventory security status.
Strategy 2: Price Adjustment Protocols During Vulnerability Windows
Temporary discount structures ranging from 5-15% for unpatched inventory provide wholesalers with flexible pricing mechanisms that acknowledge security risks while maintaining inventory turnover during vulnerability disclosure periods. These price adjustments should reflect the severity levels of the 129 fixed bugs, with devices affected by the actively exploited CVE-2026-21385 receiving deeper discounts compared to those impacted only by moderate-severity vulnerabilities. Wholesalers can implement tiered pricing structures that automatically adjust based on patch availability timelines, ensuring that Samsung, Xiaomi, and OnePlus devices receive appropriate pricing consideration during their extended manufacturer testing periods.
Bundle value-adds such as complementary security software packages or extended warranty coverage help offset security concerns while maintaining profit margins on vulnerable device inventory. Transparent communication protocols should clearly explain patch deployment timelines to retail partners, building long-term trust through honest assessment of security update availability across different manufacturer ecosystems. Successful wholesalers are creating security status dashboards that provide real-time visibility into patch deployment progress, enabling retailers to make informed purchasing decisions while demonstrating the wholesaler’s commitment to security transparency and inventory management excellence.
Strategy 3: Security-First Merchandising Approaches
Making security patch status a highlighted selling feature transforms the traditional electronics wholesale model by positioning security updates as premium product differentiators rather than operational burdens. Wholesalers can create competitor comparison charts that demonstrate Google Pixel’s immediate patch availability versus the extended testing timelines required for devices using the 235 affected Qualcomm chipsets from other manufacturers. These merchandising materials should emphasize how quickly different manufacturers addressed the 7 critical kernel escalation vulnerabilities and the CVE-2026-0047 Framework component flaw, helping retailers understand the security response capabilities of their preferred device brands.
Educational materials including in-store security awareness resources enable retail partners to communicate effectively with end customers about the importance of the March 2026 security bulletin and the 129 vulnerability fixes it addressed. Wholesalers should provide technical training materials that explain the integer overflow characteristics of CVE-2026-21385 and the memory corruption risks associated with the actively exploited zero-day vulnerability. These educational initiatives help retail staff confidently discuss security features with customers while positioning the wholesaler as a knowledgeable security partner rather than simply an inventory supplier, creating stronger business relationships and increased customer loyalty.
Transforming Security Challenges into Sales Opportunities
The record-breaking 129 vulnerabilities in the March 2026 Android security bulletin present electronics wholesalers with unprecedented opportunities to differentiate themselves through comprehensive Android security updates expertise and proactive mobile device management services. Creating a 24-hour vulnerability response protocol enables wholesalers to immediately assess inventory impact when future security bulletins are released, providing retail partners with faster security assessments than competitors who lack systematic vulnerability tracking capabilities. This rapid response capability becomes particularly valuable when dealing with actively exploited zero-day vulnerabilities like CVE-2026-21385, where quick identification of affected inventory can prevent customer security incidents and maintain retailer confidence.
Forward-thinking wholesalers are positioning themselves as “security-conscious” suppliers by implementing future-proofing strategies that build security update guarantees directly into vendor contracts and customer agreements. These contractual commitments can include specific timelines for security patch verification, guaranteed inventory replacement for devices with critical vulnerabilities, and preferential pricing for retailers who prioritize security-patched inventory over discounted vulnerable devices. The complexity of managing patches across Android Open Source Project versions 14, 15, 16, and 16-qpr2 creates natural barriers to entry that established wholesalers can leverage to demonstrate superior technical capabilities and build stronger relationships with security-aware retail partners seeking reliable mobile device management expertise.
Background Info
- Google released the March 2026 Android Security Bulletin on March 3, 2026, addressing a record-breaking total of 129 security vulnerabilities across the Android ecosystem.
- The bulletin includes a patch for CVE-2026-21385, a high-severity zero-day vulnerability located in an open-source Qualcomm Graphics subcomponent that was confirmed to be under “limited, targeted exploitation” by attackers.
- CVE-2026-21385 is technically classified as an integer overflow or wraparound flaw that allows local attackers to trigger memory corruption and potentially gain elevated privileges.
- The vulnerability affects 235 different Qualcomm chipsets, impacting a wide range of devices including smartphones, tablets, and foldables from manufacturers such as Samsung, Xiaomi, OnePlus, Motorola, and Nokia.
- Google’s Threat Analysis Group alerted Qualcomm to the flaw on December 18, 2025, and Qualcomm subsequently notified its customers regarding the issue on February 2, 2026.
- In addition to the active zero-day, the update addresses 10 critical severity vulnerabilities within the System, Framework, and Kernel components that could lead to remote code execution, privilege escalation, or denial-of-service conditions without requiring user interaction.
- Specific critical flaws patched include CVE-2026-0006, a remote code execution vulnerability in the System component requiring no additional privileges, and CVE-2025-48631, a denial-of-service flaw also located in the System component.
- Seven critical escalation of privilege flaws were identified and patched within Kernel components, alongside CVE-2026-0047, an escalation of privilege vulnerability in the Framework component.
- Google issued two distinct security patch levels for this bulletin: 2026-03-01 and 2026-03-05, with the latter date bundling all fixes from the initial release plus additional patches for closed-source third-party and kernel subcomponents.
- The updates apply to Android Open Source Project (AOSP) versions 14, 15, 16, and 16-qpr2, though availability varies by device manufacturer due to testing and hardware configuration requirements.
- “There are indications that CVE-2026-21385 may be under limited, targeted exploitation,” Google stated in its official March 2026 Android Security Bulletin.
- “We commend the researchers from Google’s Threat Analysis Group for using coordinated disclosure practices,” a Qualcomm spokesperson told BleepingComputer regarding the GPU-related research and subsequent fixes made available to customers in January 2026.
- The update also resolves issues in components provided by MediaTek, Arm, Unisoc, Imagination Technologies, and various OEMs, which may not affect all Android devices depending on their specific hardware configurations.
- Severity levels for the 129 fixed bugs range from Moderate to Critical, with multiple flaws explicitly marked as high risk for unauthorized access, surveillance, or malware installation.
- Previous reports indicate that Google patched two other high-severity zero-day vulnerabilities, CVE-2025-48633 and CVE-2025-48572, in December 2025, both of which were similarly tagged as being under limited, targeted exploitation.
- Users are advised to install the update immediately via Settings > Security & privacy > System & updates > Security update, as delaying the patch leaves devices vulnerable to exploits that can occur without visible symptoms.
- While Pixel devices receive these security updates immediately, other vendors often require additional time to test and tweak the patches for specific hardware configurations before rolling them out to end users.
Related Resources
- Helpnetsecurity: Android’s March 2026 security patch fixes…
- Nokiapoweruser: Google’s March 2026 Android Security Update…
- Techrepublic: Google’s Biggest Android Security Update in…
- Lifehacker: Update Your Android ASAP to Patch These 129…
- Forbes: Critical Android Update—Google And CISA Confirm…